From blind spots to full clarity: How Continuous Asset Visibility transforms network security
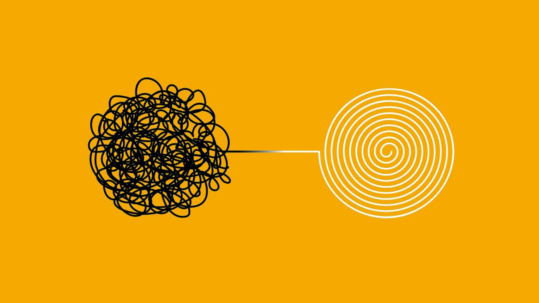
In today’s ever-changing network landscape, staying ahead of potential risks and ensuring robust security measures is crucial. This task becomes even more challenging with the constant influx of devices, applications, and user connections. However, a solution known as Continuous Asset Visibility and Security (CAVS) offers a transformative approach that provides organisations with a holistic view of their network assets. By analysing data points and assessing potential risks, CAVS empowers businesses to make informed decisions and take swift action when needed.
The dynamic nature of networks
Networks are dynamic entities, continuously evolving with new devices being added and old ones being removed. To ensure secure access for users, detect malicious activities, and plan for future growth, real-time tracking of these changes is essential. Network asset visibility solutions play a crucial role in achieving this by enabling continuous monitoring of all devices connected to the network, ranging from physical and virtual machines to endpoints like laptops, tablets, and smartphones. Furthermore, IoT devices, such as detection systems and CCTV security camaras, can be monitored, offering comprehensive coverage.
Understanding the network: The first step to effective management
Effectively managing a network begins with understanding its composition. Identifying the devices present on the network, the applications running on them, and the data flowing through the infrastructure are vital pieces of information. However, in large-scale environments with thousands of endpoints, gaining this understanding can be challenging. Fortunately, Continuous Asset Visibility and Security (CAVS) provides a solution by offering a holistic view of all devices and applications present on the network.
The power of Continuous Asset Visibility and Security (CAVS)
CAVS acts as a catalyst in comprehending networks and taking proactive action. By consolidating data from various sources, CAVS allows organisations to analyse data points collectively and evaluate potential risks. It goes beyond mere data collection and provides alerts based on user-defined rules, enabling swift response to issues such as slow assets or non-compliance with established service level agreements (SLAs). With CAVS, businesses can make informed decisions and prioritise actions based on a comprehensive understanding of their network assets.
Streamlining operations with complete asset visibility
Fragmented security data often hampers organisations, leading to challenges in asset management and security operations. However, CAVS eliminates the need for manual cross-referencing and offers complete asset visibility. Seamlessly integrating with existing IT and security tools, CAVS aggregates, deduplicates, and normalises data for every asset in the environment. This unified and real-time asset inventory acts as a single source of truth, enabling streamlined operations and enhancing overall efficiency.
Contextualised asset intelligence: Prioritising action
CAVS goes beyond traditional inventory management by adding contextual intelligence to assets. With the Collective Asset Intelligence Engine, IT and security teams can prioritise remediation efforts based on risk and criticality. Armed with these insights, organisations can make informed decisions, taking action where it matters most and allocating resources effectively.
Effortless compliance through automated policy enforcement
Meeting compliance requirements is a significant challenge for organisations. With CAVS, the process becomes more manageable through automated policy enforcement. Organisations can define policies that enforce security controls across all devices, triggering vulnerability scans and facilitating compliance with industry regulations and standards seamlessly.
Continuous Asset Visibility and Security (CAVS) represents a ground-breaking approach to network security. By providing a holistic view of devices and applications, CAVS enables organisations to assess potential risks and respond swiftly to issues. It streamlines operations, enhances compliance efforts, and empowers organisations to achieve effective cybersecurity asset management.
For more information please contact our cybersecurity professionals today.
Recent news
Latest posts
Key Strategies and Best Practices for Enhancing OT Security
05 April, 2024A Comprehensive Guide to Third Party Risk Management (TPRM)
26 February, 2024