The Essential 8 cybersecurity strategies your business needs for compliance
The Federal Government is about to change the rules on cybersecurity, and your business needs to take notice.
In late October 2022, Attorney General Mark Dreyfus announced the plan to raise the fine for any company’s serious or repeated breaches of the Privacy Act to about $50 million – up from $2.2 million. Recent breaches at telco Optus and health insurer Medibank that saw sensitive customer data hacked have prompted the move, with Dreyfus saying, “existing safeguards are inadequate”.
The Australian Financial Review says fines could surpass $50 million, depending on the company’s turnover and the estimated value of stolen data.
Here’s what your business can do to help keep compliant when it comes to cybersecurity.
These measures are robust. They centre on the implementation strategies for the ‘Essential 8 Framework’ by the Australian Cyber Security Centre (ACSC). But hackers are usually one step ahead. So, while these measures are a great baseline, they won’t guarantee total protection.
The ACSC says no single set of mitigation strategies will protect all organisations against all cyber threats. Each business is unique.
The Essential 8
These measures were introduced in June 2017 and most recently updated in July 2022. They were developed with the aim of protecting Microsoft Windows-based internet-connected networks. (The ACSC has alternative guidance for Cloud Services, Enterprise Mobility, or other operating systems, such as Apple iOS and Apple macOS.)
Here’s the list of mitigation strategies:
1. Control applications on workstations and servers to restrict executions, such as those of software libraries, scripts, HTML applications
2. Patch application security vulnerabilities within two weeks of release or 48 hours if there’s a breach
3. Configure Microsoft Office macro settings to what users need
4. User application hardening, so web browsers don’t process Java or web ads from the internet
5. Restrict administrative privileges with a clear policy and processes
6. Patch/update operating systems for security vulnerabilities within two weeks of release or 48 hours if there’s a breach
7. Multi-factor authentication is the default
8. Regular backups of important data, software, and configuration settings
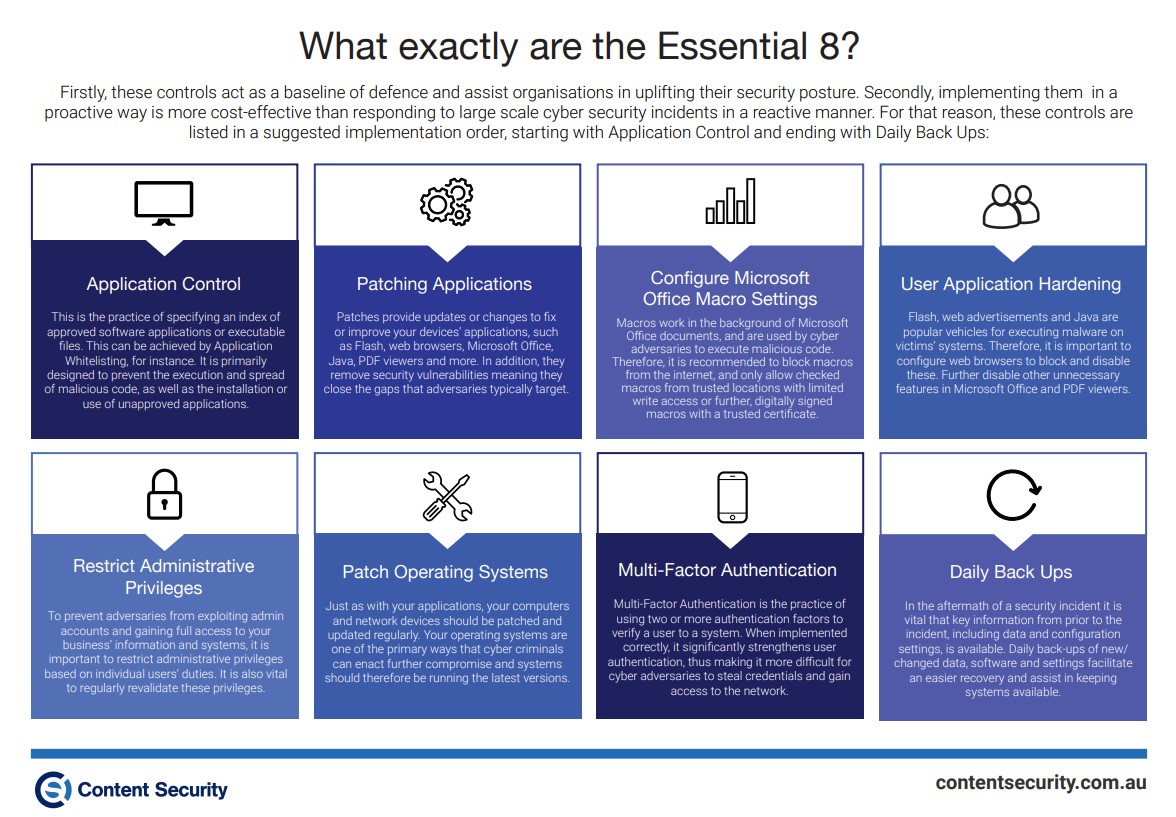
The Essential 8 dovetail into each other to help create a virtual mesh to protect your business against cyber threats. Do a deep dive into each of the Essential 8 here – there’s quite a lot to them. And, ACSC’s Ransomware Action Checklist is handy to have as part of your arsenal.
Cyber security rating your business
Can your company tick off each of the Essential 8 elements? That’s where the framework’s maturity scale comes in.
· If your business has weaknesses in its overall cyber security stance that risk your data confidentiality, system integrity, or availability being compromised, that’s Maturity Level 1
· If you’re partially aligned with the above measures, you’re still sitting at Maturity Level 1
· If you can tick off most of them, you’ve hit Maturity Level 2, and
· If you meet them all, congratulations, you’re at Maturity Level 3.
Maturity Level 3 means you’re optimising protection against malware threats and cyber attacks, which should be your goal, according to the Australian Signals Directorate. You can find out more about the Maturity Levels here.
For more information please contact our cybersecurity professionals today.
Recent news
Latest posts
Key Strategies and Best Practices for Enhancing OT Security
05 April, 2024A Comprehensive Guide to Third Party Risk Management (TPRM)
26 February, 2024